I am Benjamin Johnston, a tech lead / developer, a researcher and an educator.
I work in artificial intelligence, web development, cloud, innovation, entrepreneurship, artificial commonsense reasoning and social robotics.
I occasionally post short articles of interest to a general audience here.
Stalling for time with LLMs
In conversation, sometimes it’s useful to stall for time. For example, saying, “that’s a great question,” gives you a moment to consider your response.
In interactive voice systems, the same principle applies. Rather than a system pausing silently for a few seconds while completing speech recognition, it can be more natural for the system to begin responding to show that it has heard the speaker.
It is possible to have a few generic templates such as “Hmmm. Let me think.” However, I’ve found LLMs can be used to generate more specific fillers.
Read on for details.
Continue Reading (Published 7 December 2023)
GPT-3 versus IBM Watson
Could GPT-3 (or ChatGPT) beat IBM Watson in Jeopardy!?
I used the clues from both rounds of both games of the Jeopardy! IBM Challenge.
I scripted each question with a simple prompt and then manually compared with the correct responses.
Read on to see the results.
Continue Reading (Published 31 December 2022)
Full Stack Web Development
I have taught a class on full stack web deveopment using JavaScript/TypeScript at the University of Technology Sydney. The subject is called “Advanced Internet Programming”.
As an accompaniment to the course, I prepared a free online workbook/textbook that is now available online.
The materials cover the internals of web technologies, good design principles, best practices, distributed systems and teamwork.
(Published 27 May 2021)
Prototyping grammars in JavaScript / TypeScript
Context-free grammars are a popular technique for parsing input in software development. Implementing a grammar can be difficult or require complex dependencies. Ambiguous and recursive grammars can be particularly challenging.
Read on for a technique I like to use when rapidly prototype grammars in JavaScript or TypeScript.
The technique uses yield to simulate Prolog's definite clause grammars in JavaScript.
Continue Reading (Published 25 January 2021)
Intentionally Insecure Web App
BunchOfFriendsJS is an intentionally insecure social network to teach web security.
I recently redesigned and reimplemented the system for Node.js, based on an earlier version designed for Java EE.
It is designed to have many of the OWASP Top 10 vulnerabilities.
To run BunchOfFriendsJS:
- Ensure a recent version of Node.js is installed
- Ensure you have no services running on port 3000
- Run
npx bjau/bunchoffriendsjsand open your browser to http://localhost:3000/ (thenpxcommand will automatically download and run a temporary version)
Continue Reading (Published 12 September 2020)
Hospital Wayfinding

We recently conducted a research study with social robots at Fairfield hospital in Sydney.
We designed the experience and then implemented the intelligent distributed system. It combines a Softbank Pepper robot, a touch screen kiosk and several edge computing devices.
The robots alleviate stress and contribute to the welcoming atmosphere at the hospital.
Continue Reading (Published 20 March 2020)
World Champions at RoboCup

UTS Unleashed! are the world champions in the @Home Social Standard Platform League at RoboCup 2019.
We programmed our Pepper robots to solve challenging problems in the home: working as a housekeeper, tour guide, party host and waiter.
Continue Reading (Published 8 July 2019)
Most Surprising Pronunciations
Grapheme-to-Phoneme (G2P) conversion is the process of translating written characters (e.g., "hello") into phonemes that indicate how to pronounce the word (e.g., HH AH L OW or HH EH L OW).
English has so many quirks that state-of-the-art performance has error rates as high as 20%–30%. See, for example, CMU Sphinx's g2p-seq2seq. I'm currently working on a small and embeddable G2P system.
An interesting application of G2P is finding words that have surprising pronunciations.
Just for fun, below is a list of the 250 words that my G2P system found most surprising.
Continue Reading (Published 15 May 2019)
Faster Matrix Multiplications in Numpy
Matrix multiplications in NumPy are reasonably fast without the need for optimization. However, if every second counts, it is possible to significantly improve performance (even without a GPU).
Below are a collection of small tricks that can help with large (~4000x4000) matrix multiplications. I have used them to reduce inference time in a deep neural network from 24 seconds to less than one second. In fact, in one case, my optimized code on a CPU turned out to run faster than Tensorflow using a GPU (1 second vs 7 seconds).
Continue Reading (Published 21 January 2018)
A JSP quirk
In JavaServer Pages, expressions are escaped by “<%=” and “%>”.
For example, <%= 1 + 1 %> would output 2.
On the Tomcat web server, JSP gets translated into a servlet. The above expression declaration is implemented as a translation into the following line of Java code embedded in a Servlet:
out.print( 1 + 1 );
According to the JSP specification, a translation error will occur if the expression inside the declaration is not well formed in the underlying language (i.e., is not a valid Java expression).
A fun quirk of JSP on the Tomcat server is that the following code doesn’t result in a compile error:
<%= ""); out.print("Hello, World!" %>
Obviously, ""); out.print("Hello, World!" is not a valid Java expression.
However, Tomcat uses a superficial syntactic translation.
Here’s what the above declaration looks like after translation:
out.print( ""); out.print("Hello, World!" );
This is valid Java, despite not being translated from a valid Java expression.
You shouldn’t and wouldn’t want to rely on this behavior. Instead, it is just a fun quirk that I like to use when teaching how JSP works under the hood.
Continue Reading (Published 19 November 2017)
Java EE course
I have been teaching a class on Java EE at the University of Technology Sydney. The subject is called “Advanced Internet Programming”.
The videos, guided practical sessions and sample solutions are now available online.
The materials cover HTTP, Servlets, JavaServer Pages, JavaServer Faces, database connectivity (JDBC), naming (JNDI), dependency injection (CDI), Enterprise JavaBeans, object-relational mapping (JPA), web services (JAX-WS and JAX-RS), asynchrony and message driven beans.
(Published 4 November 2016)
Answer Set Programming in Python
Potassco is an Answer Set Solving system. There is a native library for embedding Answer Set Solving in Python. However, the library does not work under Windows.
Fortunately, the Potassco tools can output data in JSON format. One integration option is to invoke the compiled binary directly. The PyASP Python library uses this strategy.
The same effect can be achieved in just a few lines of code:
import subprocess
import json
clingo_path = 'path\\to\\bin\\clingo.exe'
clingo_options = ['--outf=2','-n 0']
clingo_command = [clingo_path] + clingo_options
def solve(program):
input = program.encode()
process = subprocess.Popen(clingo_command, stdin=subprocess.PIPE, stderr=subprocess.PIPE, stdout=subprocess.PIPE)
output, error = process.communicate(input)
result = json.loads(output.decode())
if result['Result'] == 'SATISFIABLE':
return [value['Value'] for value in result['Call'][0]['Witnesses']]
else:
return None
Note that the clingo_path (the third line) must be set appropriately.
The output is a list of solutions, each solution is a list of strings corresponding to terms that the ASP solver could prove.
Suppose this library is named asp.py, it may be used as follows:
import asp
solutions = asp.solve('1 { a; b } 1.')
# Print out the solutions
print(solutions)
# Output: [['b'], ['a']]
(Published 11 June 2016)
Simple Solar Model
Here is a very simple tool to calculate the sun’s position in the sky. It uses a minimal model based on a few orbital parameters. Despite its simplicity, it makes predictions that are very close to more complete models.
The tool is inspired by a recent discussion I had with somebody who claims the world to be flat. He seemed otherwise sane but he genuinely believed modern science to be a lie.
I was shocked and upset for days. Not only is it a rejection of our amazing technological progress but also it represents a failure of science and engineering education.
Continue Reading (Published 8 January 2016)
Jyroscope (rosjava alternative)
ROS (Robot Operating System) is currently the most popular platform for robot development. On ROS, the de facto standard for Java development is a package called rosjava.
I have created an experimental alternative to rosjava that I call Jyroscope. Jyroscope makes it easier to write ROS code using Java.
- It uses dependency injection to wire up publishers and subscribers.
- It does not have any external dependencies.
- It does not require any particular build system. It works with javac or any IDE. It can be embedded in another project by copying the source code.
- It does not require any message generation. Mappings between Java and ROS messages are resolved at runtime.
- It uses Java-to-ROS and ROS-to-Java translators that are compiled at runtime to maintain efficiency and speed.
- It implements TCPROS protocols directly so it works with any version of ROS (until ROS switches to DDS).
- It is free to use however you wish -- it is under a Creative Commons Zero / Public Domain license.
I’ve been using it for a number of small projects but the code is very much experimental:
- It is only a prototype / technology-concept.
- It is not documented or tested.
- It only supports publishing and subscribing.
- It must be run on a full Java 8 JDK (not just a JRE).
- It does not implement future ROS 2.0 DDS-based protocols.
You can download the full source from Github
In the remainder of this article, I will demonstrate how to use Jyroscope.
Continue Reading (Published 12 December 2015)
Unvalidated Input Hidden in JSF
When developing complex applications, JavaServer Faces (JSF) works best when used “statefully”.
In practice, this means using @ViewScoped backing beans.
A consequence is that client-specific view state is persistent on the server.
JavaServer Faces can also be used in a stateless mode.
Unfortunately, stateless operation presents problems when using validation. In particular, validation failures prevent model update. This means that model state cannot be used to render a view in the event of a validation error.
Input components can use posted-back form data to re-render the view during a validation error.
However, output components (e.g., <h:outputText>) have no posted-back data.
Their state needs to be maintained using hidden fields in a form.
In JSF, hidden state can be maintained using <h:inputHidden>.
However, validation interferes with <h:inputHidden>.
Like any other input component, validation errors prevent all model updates.
My solution to this problem is to use a custom component.
The component works almost the same as <h:inputHidden>.
Instead of following the usual JSF lifecycle, it performs model update before validation.
Read on for the implementation and an example of its use.
Continue Reading (Published 6 September 2015)
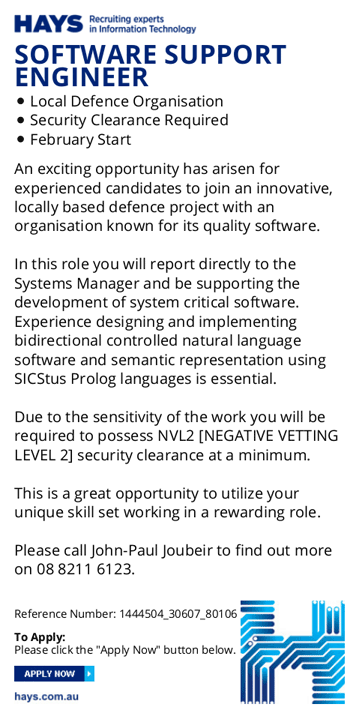
The Job Market for Prolog (Part 2)
Eleven years ago, I set up keyword alerts for “Prolog” on the major Australian career websites.
For ten years, there was no match. Until one-and-a-half years ago, when I reported a match on this blog.
I've just got another match. I believe that two Prolog jobs in 18 months counts as a boom in the Prolog job market!
Look out, Java. Look out, C#. Look out, Python. Prolog is taking over.
The advertisement disappeared quickly, but I took a few screen-grabs with my phone. I've stitched them back together below (and added the red circle).
Continue Reading (Published 29 July 2015)
Smartphone vs Loaf of Bread
In Sydney, it is possible to order a single loaf of bread from an “artisan” bakery for around $15. A fully featured Android smart phone or Windows Phone can be purchased for just over $30.
One smartphone for the price of two loaves of bread.
This smartphone price will, no doubt, come down. The bread prices will, no doubt, increase.
It won’t be long before a loaf of bread you order online will cost more than the computer you used to place the order.
(Published 3 July 2015)
Reading the Binary Screens

The University of Technology, Sydney recently opened a new building (the ‘Broadway building’). It was created for the Faculty of Engineering and IT. It is wrapped in aluminium screens that are perforated with binary code. The university has a video about it on YouTube.
What do the screens say? How are they encoded? Read on for an explanation.
Continue Reading (Published 19 April 2015)
Minimal ASP.NET Identity
Visual Studio 2013 has several templates for creating new web projects. A brand new web project with authentication will have over 1500 lines of C# code. This saves a lot of time for new applications.
1500 lines for authentication may be too much if you’re learning ASP.NET. Fortunately, ASP.NET Identity is not too complicated when you start “from scratch”.
What follows is a short tutorial on setting up basic ASP.NET Identity in an empty web project.
Continue Reading (Published 28 March 2015)
Discarded Apple Newton
This is a photograph of an Apple Newton that I noticed was lost/discarded in a park near my home today.

The hand-held computer is almost 20 years old. In fact, it might be regarded as a museum piece.
It doesn’t make sense to hold onto such a device for so long and then just discard it in the park.
I like to imagine it was owned by a die-hard Newton fanatic. Perhaps he or she felt that no modern smart phone or tablet could rival the classic. Thus, it was left in the park by accident.
For this reason, I left the Newton for their return. I can only hope that the original owner was joyfully reunited with their device.
(Published 8 March 2015)
Church Numerals in C#
This is a just-for-fun post. I’ll explore a C# implementation of a theoretical system called Lambda calculus.
It certainly isn’t practical. A calculation of the 25th Fibonacci number (75025) is not complex. An efficient algorithm can calculate it in just a few CPU cycles. A naïve recursive function can calculate it in 3 milliseconds. However, using Church numerals in a Lambda calculus takes 2300 times longer (7100 milliseconds).
The exercise may be pointless from a pragmatic perspective. However, it is interesting to see that the theory can be translated so directly into working C# code.
Continue Reading (Published 1 March 2015)
Intentionally Insecure Web App
Updated 2015-09-25
BunchOfFriends (formerly named FriendFace) is an intentionally insecure social network to teach web security. It was developed for Java EE 7 and a Derby/JavaDB or MySQL database. It has been tested on the GlassFish 4.1 app server. It is designed to have many of the OWASP Top 10 vulnerabilities.
Download BunchOfFriends:
- Compiled WAR for deployment
- JavaServer Faces source files as a zipped NetBeans project for development
- GitHub Project for development
Before deployment: Create a JDBC resource named “jdbc/aip” (without the quotes). On each deployment, the application will automatically (re)create database tables and pre-populate them with sample data.
Requirements: JavaDB or MySQL is required (for other databases, you'll need to modify SampleData.java). Java EE version 7 is required so you'll need GlassFish version 4.1 (or higher) or an equivalent application server. It should also work on GlassFish 4.0 if you upgrade GlassFish to use JSF/Mojarra version 2.2.2 or higher. One way to ensure these dependencies is to download the Java EE download bundle of Netbeans. In Netbeans, you can create JavaDB databases, launch GlassFish and open the domain admin console from the Services tab.
Purpose: I created the system while teaching a subject on advanced internet programming. It is intended to help teach a security mindset. Feel free to use it for any purpose. However, you should not deploy it on a publicly accessible server because it is so insecure.
License: Feel free to use it however you wish - it is under a Creative Commons Zero / Public Domain license.
BunchOfFriends is an alternative to the OWASP WebGoat project. WebGoat is tutorial oriented: it is a set of guided exercises. In contrast, BunchOfFriends is an ordinary application that is full of security holes.
BunchOfFriends can be used to re-create something like the “Samy” MySpace worm. You can create a profile that virally becomes friends with anybody who sees the profile name.
In the following is a discussion of how the OWASP Top 10 vulnerabilities relate to the application.
Continue Reading (Published 28 December 2014)
JSF Design Pattern
JavaServer Faces is a component-based MVC framework for Java web development. It is the “officially endorsed” web framework in Java EE 7.
JavaServer Faces applications have an unusual structure.
To explain, first consider the difference between using the iterator and visitor design patterns. Assume you want to sum the elements of a list. With an iterator, your code takes an active role. It would request (pull) each element of the list one-by-one. It would then update the total using each element it retrieves. In contrast, a visitor takes a more passive role. You would implement a visitor class that updates a total for every element it receives. The list is then responsible for passing (push) each element to the visitor.
What makes JavaServer Faces applications unique is that their controllers are typically very passive. The controllers in most other MVC frameworks are typically very active. They orchestrate most aspects of transforming inputs into a view. In contrast, in a JavaServer Faces application, the container does most of the orchestration. This inversion of control causes most JavaServer Faces applications to use a design pattern in which the application model is exposed as JavaBeans properties of the controller.
I teach a class on Java EE development. I try to relate design decisions to design patterns. However, I could not find any pattern catalog with a design pattern that resembles JavaServer Faces.
Continue Reading (Published 5 December 2014)
Prolog Web-scraping
In 2005, on comp.lang.prolog, I claimed that Prolog is excellent for screen-scraping web-pages. Last week - almost decade later - I received an email asking, “Why?”
The internet never forgets!
My claim was based on Prolog’s powerful pattern matching features. In Prolog, pattern matching is referred to as unification.
Assume we have a variable called Page whose value is as follows:
Page = html(body(h1('Sydney Weather'), p('Sunny')))
Then if we have a variable called Forecast we can match it to a value using the following command:
html(body(_, p(Forecast))) = Page
Prolog will ‘unify’ both sides and output the result that Forecast = 'Sunny'.
Pattern matching (or unification) is central to screen-scraping. In the remainder of this article I’ll show how to combine unification with a HTTP and HTML parser. I’ll then look briefly at the potential for natural language parsing.
Continue Reading (Published 31 May 2014)
ASP.NET MVC Cheat Sheet
I am currently teaching enterprise development with .NET.
I created this cheat sheet as a quick reference for ASP.NET MVC lab sessions. It includes Entity Framework, Validation, Razor and Controllers.
You might also find it useful.
(Published 16 May 2014)
JavaScript Robots
I fear there is a public perception that robots are too "complicated". It is true that some problems are difficult. However, the basics are very accessible. It has never been easier to get started with robotics.
Programming a robot is literally as easy as creating a web-page.
I’ve recently been using the Sphero robot toy as a way to introduce people to robotics. Sphero works well with several technologies: Ubuntu, ROS, rosbridge, sphero_ros. These technologies make it easy to program complex robot behaviors. Because the technologies are standardized, the same programs can be used on other robots, including the PR2.
In the reminder of this article, I will walk through the process of installing these technologies. Once they are all installed, I’ll demonstrate how to program and control Sphero using JavaScript in a web page!
Continue Reading (Published 9 March 2014)
Audio-feedback Speedometer
Should cars use sound instead of a dashboard?
Speedometer checks take attention away from the road. Audio could communicate the current speed without the driver needing to check the dashboard. It seems reasonable that, with audio feedback, a driver should spend less time looking away from the road.
I put this to the test and it turns out that, no, audio is distracting and annoying.

To prototype the idea, I purchased a Kiwi2 Bluetooth adapter made by PLX Devices. The device plugs into the On-board Diagnostics (“OBD-II”) socket found in virtually all cars made since 1996. The OBD-II standard is designed for technicians to check engine trouble codes as well as retrieve real-time engine performance data.
Continue Reading (Published 2 February 2014)
The Job Market for Prolog
Prolog is one of my favorite programming languages. It is a very powerful language but has not had significant industry adoption (yet!).
Almost a decade ago, I set up keyword alerts for “Prolog” on the major career websites.
There is also a Project Management software system called Prolog. This resulted in many false alarms over the years. I hadn’t come across a single authentic advertisement in a decade...
... until this one (CareerOne, 5 January 2014):
I had to pinch myself to be sure I wasn’t dreaming.
(Published 1 February 2014)
Robo-hugs for Woz
Steve Wozniak is the inventor of the Apple I and Apple II. In early January, he visited our research lab to meet our robots.

In the photograph (by Srinivas Madhisetty), my software is giving Steve Wozniak a hug by a PR2 robot.
Continue Reading (Published 1 February 2014)
Markdown Metadata
My homepage is a place where I can experiment with technology as I know the “client” is tech-savvy.
When designing the technical architecture behind this site, I had three objectives:
- The site must be served from static HTML
- The site must be easy to update
- The technology must be simple and elegant
My solution is to use Markdown encapsulated in RFC822 messages.
Continue Reading (Published 26 January 2014)
Hello, World!
I have decided to start a “blog”. I will use it to highlight my current projects. I will focus on projects that are experimental, incomplete, unsuccessful or ‘just-for-fun’.
Prior versions of my personal website have had ‘static’ designs. They made it difficult to add new content. My intention is that the informality of this format will allow me to share work wouldn’t suit publication elsewhere.
So, welcome! Feel free to let me know what you think!
(Published 25 January 2014)
All Articles by Year
- 2014 (10 articles)
- 2015 (8 articles)
- 2016 (3 articles)
- 2017 (1 article)
- 2018 (1 article)
- 2019 (2 articles)
- 2020 (2 articles)
- 2021 (2 articles)
- 2022 (1 article)
- 2023 (1 article)
Major Articles
- ASP.NET MVC Cheat Sheet
- Audio-feedback Speedometer
- Church Numerals in C#
- Faster Matrix Multiplications in Numpy
- Full Stack Web Development
- Hospital Wayfinding
- Intentionally Insecure Web App
- Java EE course
- JavaScript Robots
- Jyroscope (rosjava alternative)
- Markdown Metadata
- Most Surprising Pronunciations
- Prolog Web-scraping
- Reading the Binary Screens
- Stalling for time with LLMs
- World Champions at RoboCup